Guide on Adding, Modifying, and Deleting User Accounts in AlmaLinux
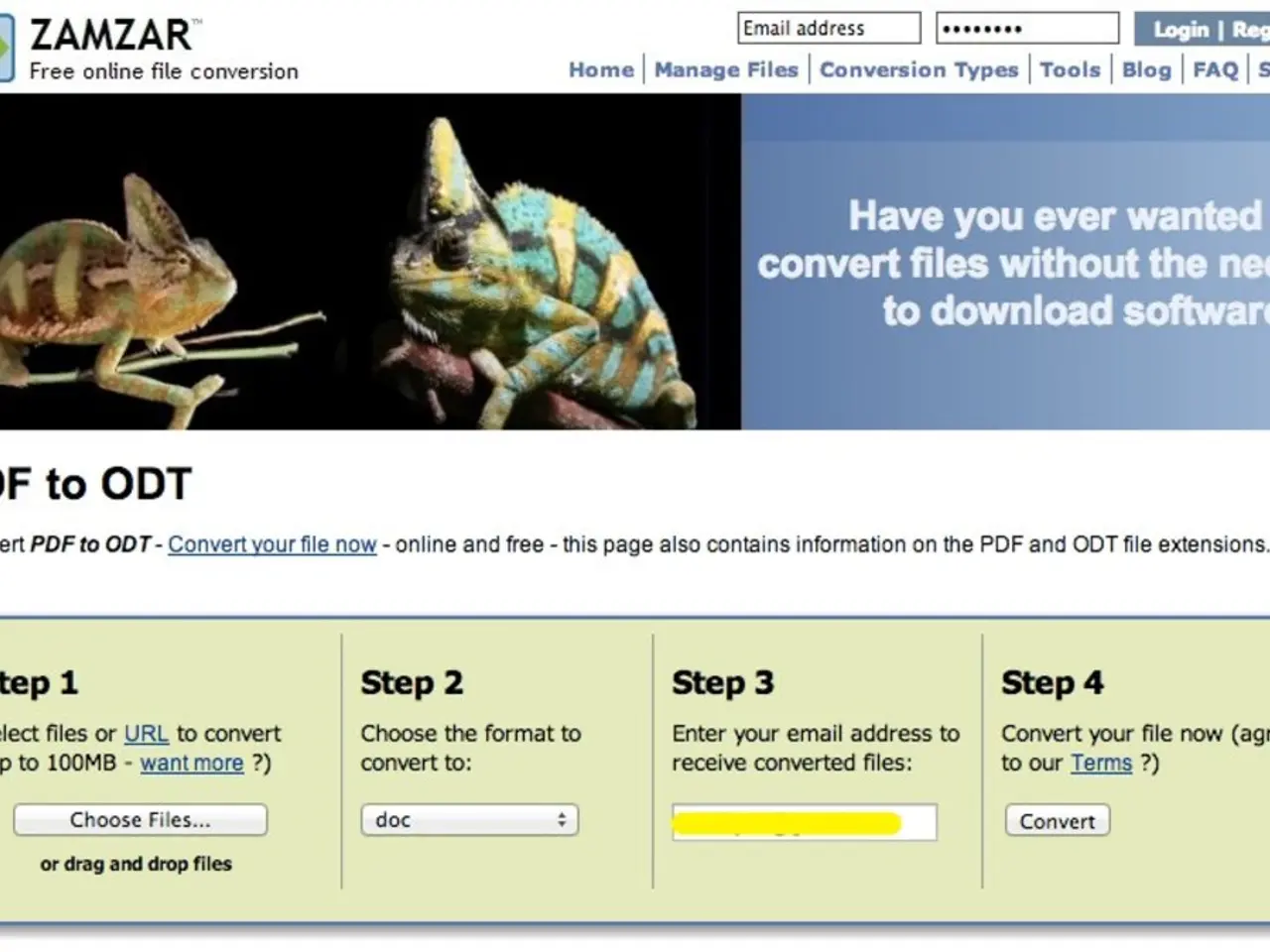
In the realm of server management, AlmaLinux 9 offers a host of tools to streamline operations and ensure security. One such tool is the Admin Console Cockpit, a web-based interface for system management. Here's a step-by-step guide on how to activate and use it.
**Activating and Using the Admin Console Cockpit**
1. **Install Cockpit and related packages:** Cockpit, a web-based interface for system management, can be installed along with useful modules like cockpit-machines (for virtual machines) and cockpit-podman (for containers) using the following command:
```bash sudo dnf install cockpit cockpit-machines cockpit-podman ```
2. **Enable and start the Cockpit service socket:** Once installed, enable the cockpit socket to start Cockpit on boot and start it immediately:
```bash sudo systemctl enable --now cockpit.socket ```
3. **Verify Cockpit service status:** Check that the Cockpit socket is active and listening:
```bash systemctl status cockpit.socket ```
You should see an "active (running)" status indicating Cockpit is running.
4. **Access the Cockpit Web UI:** Open a web browser and go to:
``` https://
Use your system credentials to log in, and you will have access to the Admin Console dashboard, where you can monitor system performance, manage virtual machines, storage, containers, and other system settings.
**Best Practices for User Management**
1. **Principle of Least Privilege:** Only grant users the minimum privileges necessary for their tasks. 2. **Regular Users:** Standard accounts with limited permissions. 3. **Groups:** Collections of users that can be assigned specific permissions. 4. **Troubleshooting Common Issues:** - Home directory issues: Ensure proper ownership and permissions on the user's home directory. - Sudo access not working: Verify the user's entry in the sudoers file and group memberships. - User can't log in: Check the user's password, shell, and home directory permissions.
5. **Advanced User Management Techniques:** - Add a new user account: Use the `useradd` command or the `adduser` command. - Root User: The superuser account with full system privileges. - Implement SSH Key Authentication: For remote access, consider using SSH keys instead of passwords. - Using Access Control Lists (ACLs)
6. **Security Measures:** - Secure the Root Account: Avoid using the root account directly; use sudo for administrative tasks. - Monitor User Activities: Use tools like `auditd` to track user actions, especially for privileged accounts. - Setting Up Password Aging with PAM (Pluggable Authentication Modules)
Understanding user management capabilities is crucial for managing servers, multi-user workstations, and modifying existing user accounts. Implementing these best practices will help ensure a secure and efficient server environment in AlmaLinux 9.
Data security is vital for proper server management, and AlmaLinux 9 provides the Admin Console Cockpit, a web-based interface for system management, to enhance security. To activate and use this tool, you must install Cockpit and related packages, enable and start the Cockpit service socket, verify its status, and access the web UI.
In data-and-cloud-computing, education-and-self-development, mastering user management techniques is essential to ensure a secure and efficient server environment. User management best practices in AlmaLinux 9 include applying the principle of least privilege, managing groups, troubleshooting common issues, and adopting advanced techniques like SSH key authentication and ACLs.
Lastly, technology evolves, and it's essential to stay informed and continue learning about recent security measures such as secure root account management, monitoring user activities using auditd, and setting up password aging with PAM (Pluggable Authentication Modules). Knowledge in these areas is crucial for maintaining a robust and secure data infrastructure.